Computer
What is the difference between booting and starting?

Introduction
In the realm of technology, we often encounter terms that might seem interchangeable at first glance, but upon closer inspection, they reveal distinct processes and functions. Two such terms are “booting” and “starting.” These terms are frequently used when discussing computers, operating systems, and even everyday gadgets. In this article, we will delve into the intricacies of booting and starting, shedding light on their differences, functions, and significance in the world of technology.
Understanding Booting
Booting Basics
Booting, often referred to as “bootstrapping,” is the initial process a computer undergoes when it is powered on or restarted. This procedure is crucial because it establishes the fundamental conditions necessary for the computer to run its operating system and applications smoothly.
Boot Sequence
The booting process generally follows a sequence of steps, starting with the moment you press the power button. These steps include hardware checks, loading the BIOS or UEFI, initializing hardware components, and locating the operating system’s bootloader.
Bootloader
The bootloader plays a pivotal role in booting. It is a small program responsible for locating the operating system’s kernel, loading it into memory, and transferring control to the kernel. The bootloader’s efficiency determines how quickly your computer can start up.
Types of Booting
Cold Boot
A cold boot occurs when a computer is powered on from a completely turned-off state. During a cold boot, the computer’s hardware and software go through a full initialization process.
Warm Boot
A warm boot, also known as a restart or soft reboot, happens when a computer is rebooted without being fully powered off. This process skips some hardware checks and is generally faster than a cold boot.
Understanding Starting
Starting an Application
Starting, on the other hand, refers to the process of launching a specific software application or program on a computer or electronic device. It is a more localized and user-initiated action compared to booting.
User-Initiated Process
Starting is entirely under the user’s control. When you decide to open a web browser, word processor, or any other software, you are essentially starting that particular application.
Multiple Instances
Unlike booting, which occurs once when the computer is powered on, starting can happen multiple times during a single computing session. You can start and close various applications as needed, and they run concurrently.
Key Differences
Booting vs. Starting
Now that we’ve explored the fundamental aspects of booting and starting, let’s highlight the key differences between these two processes:
- Initialization vs. Execution (H3): Booting involves the initialization of hardware and software, while starting focuses on the execution of specific programs.
- System-Wide vs. User-Initiated (H3): Booting sets up the entire system, while starting is user-initiated and involves running individual applications.
- Occurrence (H3): Booting happens once when the computer is powered on, while starting can occur multiple times during a session.
Conclusion
In the world of technology, understanding the difference between booting and starting is essential. Booting lays the foundation for your device to operate, while starting allows you to interact with specific applications. Both processes play integral roles in the functionality of computers and electronic devices, making them fundamental concepts for any tech enthusiast or user.
By grasping these distinctions, you can better troubleshoot issues, optimize your device’s performance, and make more informed choices when it comes to powering up your technology.
FAQs
Is booting and restart the same?
The terms boot and reboot are nearly synonymous. Start/Restart: They have nearly identical meanings. A restart, as opposed to a reset, implies to turn something on, sometimes without changing settings.
Is restarting a computer called booting?
Booting: The process of starting or restarting a computer system by loading instructions from a secondary storage device into the computer memory is called booting.
Can booting and starting be used interchangeably?
No, these terms represent distinct processes in the world of technology. Booting initializes the entire system, while starting launches specific applications.
Why is booting essential for a computer?
Booting is crucial because it sets up the hardware and software conditions necessary for the computer to run its operating system and applications effectively.
How long does the booting process usually take?
The duration of the booting process can vary depending on hardware and software configurations. It typically takes a few seconds to a minute or two.
Can I skip the booting process and start my computer directly?
No, booting is an integral part of the computer’s startup sequence. It cannot be skipped.
What’s the main difference between a cold boot and a warm boot?
A cold boot occurs when the computer is powered on from a fully turned-off state, while a warm boot is a restart without a full power-off, typically initiated by the user.
Computer
RAM vs SSD which is more important for computer performance?

Introduction
Regarding computer performance, having sufficient RAM and a fast SSD can make a noticeable difference. RAM acts as temporary storage for data that the computer actively uses, while an SSD provides long-term storage for files and programs. Both components contribute to a computer’s overall speed, responsiveness, and multitasking capabilities.
2. What Is RAM?

RAM, or Random Access Memory, is a type of computer memory that stores data and instructions the computer’s processor needs to access quickly. Since it is volatile memory, when the machine is turned off or restarted, its contents are gone. RAM allows the processor to quickly read and write data, enabling faster execution of programs and tasks.
3. RAM’s Impact on Computer Performance
RAM plays a crucial role in computer performance by providing a temporary workspace for the processor. When you open a program or file, it is loaded into RAM, allowing the processor to access the necessary data quickly. The more RAM your computer has, the more data it can store in this temporary workspace, reducing the need for frequent access to slower storage drives.
4. What Is an SSD?

An SSD, or Solid-State Drives, is a storage device that uses flash memory to store data persistently. Unlike traditional hard disk drives (HDDs) that rely on spinning disks and mechanical parts, SSDs have no moving parts, which makes them faster, more durable, and more energy-efficient. SSDs provide long-term storage for your operating system, programs, files, and documents.
5. The Role of an SSD in Computer Performance
An SSD significantly affects computer performance by providing faster read and write speeds than HDDs. When your operating system and programs are stored on an SSD, they load much quicker, resulting in faster boot and application launch times. SSDs also offer speedier file transfer speeds, enabling seamless multitasking and reducing overall system lag.
6. RAM vs SSD: Different Functions
RAM and SSD serve different functions in a computer system. RAM is a temporary workspace for operational data, allowing the processor to access it quickly. On the other hand, an SSD provides long-term storage for your files and programs, enabling faster access and retrieval than traditional hard drives.
7. Impact on Speed and Performance
Both RAM and SSD significantly impact computer speed and performance, but in different ways. RAM affects the rate of running programs and multitasking capabilities. The more RAM you have, the more data your computer can hold in its temporary workspace, resulting in smoother and more efficient operation. On the other hand, an SSD affects the speed of loading the operating system, launching applications, and transferring files. Upgrading to an SSD can dramatically reduce boot times and improve system responsiveness.
8. Choosing the Right Configuration
Choosing the correct configuration for your computer depends on your specific needs and usage patterns. Investing in more RAM is advisable if you frequently work with resource-intensive applications or multitask heavily. On the other hand, upgrading to an SSD is the way to go if you want faster boot times, quicker application launches, and improved file transfer speeds. Ideally, a combination of sufficient RAM and a fast SSD provides the best performance.
9. Upgrading RAM vs Upgrading SSD
Upgrading RAM and upgrading an SSD can both have noticeable impacts on computer performance. Adding more RAM allows your computer to handle larger datasets and run more programs simultaneously without slowdowns. Conversely, upgrading to an SSD improves system responsiveness, reduces load times, and enhances overall user experience. Depending on your specific needs and budget, upgrading one or both components can be viable.
10. How RAM and SSD Complement Each Other
RAM and SSD work together to optimize computer performance. While RAM provides temporary storage for active data, the SSD is long-term storage for files and programs. When your computer requires more data than can fit in RAM, it utilizes the SSD as virtual memory. This combination allows efficient data handling, smooth multitasking, and faster overall performance.
11. Tips for Optimizing RAM and SSD
To make the most of your computer’s RAM and SSD, consider the following tips:
Close unnecessary programs and background processes to free up RAM.
Use the operating system’s built-in tools to manage virtual memory settings.
Keep your SSD clean by regularly deleting unnecessary files and running disk cleanup utilities.
Refrain from filling up your SSD to its maximum capacity, leading to reduced performance.
Regularly update your operating system and drivers to ensure compatibility and performance optimizations.
12. Future Trends and Developments
As technology advances, the capacities and speeds of both RAM and SSD are expected to increase. New developments, such as DDR5 RAM and faster PCIe Gen4/Gen5 SSDs, promise higher performance. Additionally, emerging technologies like Intel’s Optane Memory aim to bridge the gap between RAM and storage, providing faster access to frequently used data.
Conclusion
Both components are vital for computer performance in the debate between RAM and SSD. RAM enables efficient multitasking and quick program execution, while an SSD improves overall system responsiveness, boot times, and file transfer speeds. To achieve optimal performance, it is advisable to have adequate RAM and a fast SSD in your computer configuration.
Frequently asked questions
Which is more critical, RAM or SSD?
RAM and SSD are essential for computer performance but serve different purposes. RAM affects multitasking capabilities and program execution speed, while an SSD improves overall system responsiveness, boot times, and file transfer speeds.
Do you know if I can use a computer without an SSD?
Yes, you can still use a computer without an SSD. Traditional hard disk drives (HDDs) can serve as an alternative, although they are slower in read and write speeds than SSDs.
How much RAM do I need for gaming?
The amount of RAM needed for gaming depends on the specific game requirements. However, most modern games recommend at least 8GB of RAM, and having 16GB or more can provide a smoother gaming experience.
Can I upgrade both RAM and SSD simultaneously?
Yes, you can upgrade both RAM and SSD simultaneously, which can significantly impact computer performance. Increasing the amount of RAM and switching to an SSD can provide noticeable improvements in speed and responsiveness.
Are there any compatibility issues when upgrading RAM or SSD?
When upgrading RAM or SSD, it is essential to consider compatibility with your computer’s motherboard and operating system. Ensure the new components are compatible with form factor, speed, and supported technologies to avoid compatibility issues.
What is the difference between RAM and SSD?
The main difference between RAM and SSD is speed. RAM is much faster than SSD, so it is used to store the data that is needed most often by the computer. SSDs are still faster than traditional hard drives, so they are used to store the operating system and other frequently used programs.
Which should I upgrade first, RAM or SSD?
If you are looking to improve the overall performance of your computer, then you should upgrade your RAM first. RAM is much faster than SSD, so it will have a more noticeable impact on performance. However, if you are looking to improve the boot time and loading times of your computer, then you should upgrade your SSD first. SSDs are much faster than traditional hard drives, so they will make a big difference in these areas.
How much RAM do I need?
The amount of RAM you need depends on the type of work you do on your computer. If you are a light user, then you may be able to get away with 4GB of RAM. However, if you are a heavy user, such as a gamer or video editor, then you will need at least 8GB of RAM.
How much storage do I need on my SSD?
The amount of storage you need on your SSD depends on how much data you have. If you only have a few programs and files, then you may be able to get away with a 128GB SSD. However, if you have a lot of data, such as movies, music, and photos, then you will need a larger SSD, such as a 512GB or 1TB SSD.
What are the benefits of having more RAM?
Having more RAM can improve the overall performance of your computer. With more RAM, your computer can store more data in memory, which means that it will not have to access the hard drive as often. This can lead to faster boot times, faster loading times, and better overall performance.
What are the benefits of having an SSD?
Having an SSD can also improve the overall performance of your computer. SSDs are much faster than traditional hard drives, so they can boot your computer up faster, load programs faster, and access files faster. This can lead to a much more responsive and enjoyable computing experience.
Computer
What is a firewall in cybersecurity?

In today’s digitally connected world, where data is the new gold and information travels across the web at the speed of light, ensuring the security of sensitive information has become a paramount concern. This article aims to explore one of the most fundamental aspects of cybersecurity: firewalls. We’ll delve into what firewalls are, their significance in safeguarding digital assets, and the various types and functionalities that make them a crucial component of network security.
Introduction to Firewalls
In the realm of cybersecurity, firewalls serve as the first line of defense against a barrage of cyber threats. They act as sentinels, monitoring and controlling the traffic entering and leaving a network. Without firewalls, a network would be like a fortress with no guards.
History of Firewalls
In order to regulate and safeguard access to internal resources, firewalls are a crucial component of computer security. Throughout the development of the Internet, they have progressed from straightforward packet filtering to more complex varieties.
The history of firewalls can be traced back to the early 1980s, when the Internet was still in its early stages of development. At the time, there was a growing concern about security vulnerabilities in the nascent network, and researchers began to develop ways to protect networks from unauthorized access.
One of the earliest firewall designs was developed by researchers at Digital Equipment Corporation (DEC) in 1987. This firewall, known as a packet filter, inspects incoming and outgoing packets based on their IP addresses and port numbers. If a packet did not match any of the firewall’s rules, it was dropped.
Packet filters were relatively simple to implement and manage, but they had some limitations. For example, they could not differentiate between different types of traffic, such as web traffic and email traffic. This could lead to blocking legitimate traffic or allowing malicious traffic to pass through the firewall.
In the early 1990s, a new generation of firewalls emerged, known as application-layer firewalls. These firewalls were able to inspect traffic at the application level, which allowed them to differentiate between different types of traffic and block malicious traffic more effectively.
Application-layer firewalls were more complex to implement and manage than packet filters, but they provided a higher level of security. As a result, they quickly became the preferred choice for many organizations.
In the late 1990s and early 2000s, firewall technology continued to evolve. Stateful firewalls were introduced, which were able to keep track of the state of network connections and allow legitimate traffic to pass through while blocking malicious traffic.
Today, firewalls are an essential part of any network security strategy. They are available in a wide variety of forms, from simple software-based firewalls to complex hardware-based firewalls.
Here is a timeline of some of the key milestones in the history of firewalls:
- 1987: Digital Equipment Corporation (DEC) develops the first packet filter firewall.
- 1990: AT&T Bell Labs develops the first application-layer firewall.
- 1991: The first commercial firewall product is released by Checkpoint Software Technologies.
- 1993: Stateful firewalls are introduced.
- 1994: The first firewall standard, RFC 1636, is published.
- 1995: The first next-generation firewall (NGFW) is released by Palo Alto Networks.
NGFWs combine the features of packet filtering, application-layer inspection, and stateful inspection into a single device. They also offer a variety of other features, such as intrusion prevention and web filtering.
Types of Firewalls in Cyber Security
Firewalls come in a wide variety of designs, each with unique advantages and disadvantages. The following are a few of the most popular kinds of firewalls:
- Packet-filtering firewalls: These firewalls inspect incoming and outgoing packets based on their IP addresses, port numbers, and protocols. They are relatively simple to implement and manage, but they are not as effective at blocking malicious traffic as other types of firewalls.
- Circuit-Level Gateways: These firewalls keep an eye on how connections are established to make sure that only valid connections are accepted.
- Stateful inspection firewalls: These firewalls keep track of the state of network connections and allow legitimate traffic to pass through while blocking malicious traffic. They are more complex to implement and manage than packet-filtering firewalls, but they are more effective at blocking malicious traffic.
- Application-layer firewalls: These firewalls inspect traffic at the application level, which allows them to differentiate between different types of traffic and block malicious traffic more effectively. They are the most complex type of firewall to implement and manage, but they offer the highest level of security.
- Next-generation firewalls (NGFWs): NGFWs combine the features of packet filtering, stateful inspection, and application-layer inspection into a single device. They also offer a variety of other features, such as intrusion prevention and web filtering. NGFWs are the most popular type of firewall today because they offer a high level of security and are relatively easy to manage.
In addition to these four main types of firewalls, there are also a number of other specialized firewalls, such as cloud firewalls and web application firewalls.
How do firewalls work?
Firewalls work by inspecting incoming and outgoing network traffic and allowing or blocking traffic based on a set of rules. These rules can be based on a variety of factors, such as the IP addresses of the source and destination devices, the ports that are being used, and the type of traffic.
Different methods can be employed by firewalls to filter traffic. Among the most popular methods are:
- Packet filtering: Packet filters inspect individual packets and allow or block them based on their IP addresses, port numbers, and protocols.
- Stateful inspection: Stateful firewalls keep track of the state of network connections and allow legitimate traffic to pass through while blocking malicious traffic.
- Application-layer inspection: Application-layer firewalls inspect traffic at the application level, which allows them to differentiate between different types of traffic and block malicious traffic more effectively.
Firewalls can be implemented in a variety of different ways. Some firewalls are implemented as software that is installed on individual computers or servers. Other firewalls are implemented as hardware devices that are installed between the network and the Internet.
Here is a simplified example of how a firewall works:
- A computer on the internal network sends a request to a website on the Internet.
- The request is passed through the firewall.
- The firewall inspects the request to determine whether or not it is allowed.
- If the request is allowed, the firewall forwards it to the Internet.
- If the request is not allowed, the firewall blocks it.
Firewalls play an important role in protecting networks from unauthorized access and malicious attacks. They are an essential part of any network security strategy.
The benefits of using firewalls:
- Firewalls can help protect networks from unauthorized access.
- Firewalls can help to block malicious traffic, such as viruses, Trojans, and spyware.
- Firewalls can help to prevent data breaches.
- Firewalls can help comply with industry regulations.
How to Use a Firewall for Protection?
To use a firewall for protection, you should:
- Enable your firewall. Most firewalls are enabled by default, but it is always a good idea to check to make sure.
- Configure your firewall’s rules. Firewall rules allow or block traffic based on a variety of factors. You should configure your firewall’s rules to allow only the traffic that you need.
- Keep your firewall up to date. Firewall developers regularly release updates to patch security vulnerabilities and add new features. It is important to keep your firewall up to date to ensure that it is providing the best possible protection.
Here are some additional tips for using a firewall effectively:
- Use a strong firewall. Not all firewalls are created equal. Some firewalls offer more features and better protection than others. Choose a firewall that is appropriate for your needs and budget.
- Keep your firewall’s rules simple. The more complex your firewall’s rules are, the more difficult they will be to manage and the more likely it is that you will make a mistake. Keep your rules as simple as possible while still providing the protection that you need.
- Monitor your firewall logs. Firewall logs can provide valuable information about the traffic that is passing through your firewall. You should regularly review your firewall logs to identify any suspicious activity.
If you are not sure how to configure your firewall or how to read your firewall logs, you can consult the documentation that came with your firewall or contact the manufacturer for assistance.
Here are some examples of how you can use firewall rules to protect your network:
- Block all incoming traffic except for traffic from specific IP addresses or ports.
- Block all outgoing traffic except for traffic to specific IP addresses or ports.
- Block specific applications, such as peer-to-peer file sharing applications or online gaming applications.
- Block specific types of traffic, such as HTTP traffic or FTP traffic.
You can also use firewall rules to create different security zones for your network. For example, you could create a high-security zone for your web server and a low-security zone for your guest network. This would help to isolate your web server from the rest of your network and protect it from attack.
Configuring a firewall is a critical step in ensuring the security of a network. This involves defining rules and policies that dictate how the firewall should handle traffic.
Why Do We Need Firewalls?
We need firewalls because they help to protect our networks and devices from unauthorized access and malicious attacks. Firewalls can block malicious traffic, such as viruses, Trojans, and spyware, from entering our networks. They can also help to prevent data breaches by blocking unauthorized access to sensitive data.
Firewalls are especially important for businesses and organizations, which often have large networks and store sensitive data. Firewalls can help these organizations comply with industry regulations and protect their customers’ data.
Here are some of the specific benefits of using firewalls:
- Prevent unauthorized access. Unauthorized individuals can be prevented from accessing your network and devices by firewalls. Your data and systems may be better protected against attattacks a result.
- Block malicious traffic. Firewalls can block malicious traffic, such as viruses, Trojans, and spyware, from entering your network. This can help prevent your devices from becoming infected and protect your data from being stolen.
- Prevent data breaches. Data breaches can be avoided with the aid of firewalls, which stop unauthorized access to critical information. Data about your consumers can be protected in this way, and it can also help you abide by industry rules.
- Improve performance. Firewalls can help to impr the performance of your network by filtering out unwanted traffic. This can free up resources on your network and improve the speed and reliability of your connection.
Overall, firewalls are an essential part of any network security strategy. They can help to protect your networks and devices from unauthorized access and malicious attacks, prevent data breaches, and improve the performance of your network.
How can I choose the right firewall?
Selecting the appropriate firewall is crucial for safeguarding your network and data. Several factors should be considered when making this decision:
- Network Requirements: Assess your network’s size and complexity. Small businesses may require different solutions than large corporations.
- Budget: Determine your budget for firewall implementation and ongoing maintenance. Some firewalls are costlier but offer more robust features.
- Scalability: Ensure the firewall can grow with your network. Scalable options accommodate increased traffic and devices.
- Ease of Management: User-friendly management interfaces simplify firewall administration, reducing the risk of configuration errors.
- Security Needs: Identify the specific threats you need protection against. Intrusion prevention, content filtering, and application control may be required.
- Compliance Requirements: Depending on your industry, you may need to meet specific compliance standards (e.g., HIPAA, PCI DSS). Choose a firewall that helps with compliance.
importance of NAT and VPN
Network Address Translation (NAT) and Virtual Private Networks (VPNs) are fundamental components of firewall functionality:
- NAT: NAT allows multiple devices in a private network to share a single public IP address. It adds a layer of security by hiding internal IP addresses. It prevents direct access from the internet to internal devices, acting as a barrier between the two.
- VPN: VPNs establish secure, encrypted connections over the internet. They enable remote access and protect data in transit. VPNs are essential for maintaining privacy and security, especially when accessing sensitive information remotely.
Next Generation Firewalls (NGFW)
Next Generation Firewalls (NGFWs) are advanced firewall solutions that combine traditional firewall features with additional capabilities:
- Application Control: NGFWs can identify and control specific applications or services, allowing fine-grained control over network traffic.
- Intrusion Detection/Prevention Systems (IDS/IPS): NGFWs include advanced IDS/IPS to detect and block threats in real-time.
- Content Filtering: They offer web content filtering to block access to malicious websites and inappropriate content.
- Advanced Threat Protection: NGFWs incorporate anti-malware and sandboxing features to detect and mitigate advanced threats.
Common Firewall Vulnerabilities and Solutions
Firewalls can have vulnerabilities, such as:
- Misconfigurations: Regularly audit and update firewall rules to prevent misconfigurations.
- Zero-Day Attacks: Employ intrusion prevention systems and keep your firewall updated to protect against unknown threats.
- DDoS Attacks: Use dedicated DDoS protection services to mitigate these attacks.
- Backdoors: Regularly monitor firewall access logs and audit the configuration to prevent backdoors.
- Unauthorized Access: Implement strong authentication and access control policies.
Real-Time Applications of Firewall
Firewalls are used in real-time for various purposes, including:
- Network Security: Protecting networks from unauthorized access and cyber threats.
- Content Filtering: blocking or allowing access to specific websites and content categories in real-time.
- Intrusion Detection: Identifying and responding to potential security breaches as they occur.
- Application Control: Managing and controlling the use of specific applications or services.
Difference between a Firewall and Anti-virus
Discover the key differences between firewalls and anti-virus software, and learn how they work together to keep your computer safe and secure.
| Attributes | Firewall | Anti-virus |
| Purpose | protects networks by keeping track of and regulating incoming and outgoing traffic in accordance with pre-established regulations. | identifies, stops, and gets rid of malware from devices. |
| Functionality | acts as a firewall between trusted and untrusted networks, blocking harmful communications and illegal access. | identifies known malware signatures and unusual activity by scanning files and programs on devices. |
| Layer of Protection | It has a “Network layer” with the goal of shielding the entire network from dangers outside. | It has a “Device layer” that concentrates on guarding against malware infestations on specific devices. |
| Effectiveness | Effective in stopping harmful traffic and preventing unauthorized access, but unable to completely ward off threats. | Although effective in finding and eliminating malware from devices, it is unable to stop unwanted network access. |
| Updates | To address new threats, firewall signatures and rules are updated. | Malware detection algorithms and signatures are often updated to find new threats. |
| Cost | Implementation and upkeep costs may be high, especially for smaller firms. | Generally less expensive than firewalls, with both company and individual price choices. |
Conclusion
In conclusion, firewalls are the unsung heroes of cybersecurity. They provide the necessary protection to keep networks, devices, and sensitive data safe from a multitude of online threats. Understanding the different types and configurations of firewalls is key to building a robust defense against cyberattacks.
FAQs
Firewalls serve as a crucial barrier between trusted networks and untrusted networks, protecting against unauthorized access and various cyber threats.
No, firewalls come in different types, such as stateful, stateless, application layer, and proxy firewalls, each with its unique features and capabilities.
Configuring a firewall involves setting rules and policies to control traffic. Best practices include regular updates and security audits.
Next-generation firewalls provide advanced threat detection capabilities, offering more comprehensive protection by inspecting traffic based on applications and user identity.
No, firewalls and antivirus software serve different purposes. Firewalls control network traffic, while antivirus software scans and removes malware from your devices. Both are essential for comprehensive cybersecurity.
Computer
what is phishing in cyber security

Phishing is a pervasive threat in the realm of cybersecurity. It is a technique employed by cybercriminals to deceive individuals into revealing sensitive information or performing actions that could compromise their security. In this article, we’ll delve into the world of phishing, exploring its types, how it operates, the consequences, and, most importantly, how to defend against it.
What is phishing ?
Phishing is a malicious practice where cyber attackers impersonate trusted entities to trick individuals into revealing personal information such as usernames, passwords, credit card details, and more. This deceit is often carried out through various means, including emails, websites, or phone calls. It preys on the vulnerability of human trust.
What is phishing, and what is its purpose ?
Phishing is a type of social engineering assault in which a perpetrator pretends to be a reliable organization (such a bank, credit card company, or government agency) in an effort to dupe victims into disclosing sensitive data, like login credentials, credit card details, or Social Security numbers. Phishing assaults can be launched by email, texts, calls, social media, or even in person.
A phishing attack’s goal is to obtain personal data the perpetrator can use for fraud or identity theft. For instance, an attacker can access a victim’s bank account using stolen login information and move money out of it, or they might start new credit accounts in the victim’s name using stolen Social Security numbers.
Phishing attacks are one of the most common types of cybercrime, and they can be very effective. Attackers are constantly developing new techniques to make their phishing emails and websites more convincing, and they often target specific groups of people, such as employees of large companies or students.
Types of Phishing Attacks
Phishing attacks can take many different forms, however some of the more popular ones are as follows:
- Email phishing: This is the most common type of phishing attack, and it involves sending fraudulent emails to victims. The emails may appear to be from a legitimate organization, such as a bank, credit card company, or government agency. The emails may contain links to fake websites or ask the victim to enter their personal information directly into the email.
- Spear phishing: Spear phishing is a more targeted type of phishing attack that is directed at specific individuals or groups of people. Attackers may gather information about their victims from social media or other online sources. The emails used in spear phishing attacks are often more convincing than traditional phishing emails, as they are tailored to the victim’s specific interests or needs.
- Whaling: Whaling is a type of spear phishing attack that is specifically targeted at high-profile individuals, such as CEOs and other executives. Whaling attacks can be very successful, as the victims are often more likely to trust the emails and to have access to sensitive information.
- Smishing: Smishing is a type of phishing attack that is carried out via text message. Smishing messages are often similar to email phishing messages, but they may also contain links to malicious apps or websites.
- Vishing: Vishing is a type of phishing attack that is carried out via phone call. Vishing scammers may impersonate representatives from a legitimate organization and ask the victim to provide personal information or to download malware.
In addition to these common types of phishing attacks, there are many other variations, such as:
- Angler phishing: Angler phishing attacks are carried out via social media. Attackers may create fake social media profiles or post links to malicious content in social media groups.
- Pharming: Pharming attacks involve redirecting users to fake websites without their knowledge. This can be done by poisoning the DNS cache or by exploiting vulnerabilities in web browsers.
- Man-in-the-middle attacks: Man-in-the-middle attacks entail listening in on conversations between two people while posing as one of them. Users may be sent to fraudulent websites or have their personal information stolen using this.
How Phishing Works
Phishing works by exploiting human psychology. Attackers create emails or other communications that are designed to look like they are from a trusted source, such as a bank, credit card company, or government agency. The emails may contain links to fake websites that look like the real websites of these organizations.
If a victim clicks on a link in a phishing email and enters their personal information on the fake website, the attacker can steal that information. Attackers can then use the stolen information to commit fraud or identity theft.
Here is a typical example of a phishing attack:
- The attacker sends the victim a phishing email. The email may appear to be coming from a reputable company, like a bank.
- The email may contain a link to a fake website that looks like the real website of the bank.
- The email may ask the victim to enter their personal information on the fake website, such as their login credentials or credit card number.
- If the victim clicks on the link and enters their information on the fake website, the attacker can steal that information.
Attackers can use the stolen information to commit fraud or identity theft. For example, they may use the stolen login credentials to access the victim’s bank account and transfer money out of it, or they may use the stolen credit card number to make fraudulent purchases.
Phishing attacks can be very effective because they are designed to exploit human psychology. People are more likely to click on links and enter their personal information if they think they are communicating with a trusted source.
How To Prevent Phishing Attacks?
You can take the following actions to avoid phishing scams:
1. Study the characteristics of phishing attacks.
Attackers can carry out a phishing attack in a variety of methods. Being aware of different attack types and what they could resemble will help to lessen the likelihood of becoming a victim. You can also read about these assaults’ more recent methods to stay informed. This can assist you in avoiding any potential danger or assault.
2. Avoid clicking on links in emails
Avoid clicking on any strange links in emails that you receive. Check the email for problems by reading it from beginning to end. Multiple grammatical or typographical problems are frequently seen in phishing emails. Errors could also be present in the email’s subject line or email address. If the email appears suspicious, even if you do not uncover any mistakes, you might choose to report it. Consider personally contacting the sender to confirm that they actually sent the email if you know them.
3. Install anti-phishing plugins
Increasing cyber security is a good method to fend off future threats. Installing anti-phishing browser plugins will help you achieve this. Through prompts, these plugins can assist you in spotting possible phishing attempts. Plugins may come pre-installed on some browsers. Additionally, you can add reliable plugins to your browser by downloading them from the internet.
Related: What Is A Firewall? (With Benefits, Types And FAQ)
4. Update your passwords regularly
Think about regularly upgrading your passwords. You can do this to keep your accounts safe. Numerous websites may provide user information to third parties for marketing purposes, but doing so could make your information vulnerable to hackers. Regularly changing your passwords can stop criminals from accessing your accounts using outdated information.
Conclusion
Phishing remains a significant threat in the realm of cybersecurity. Understanding its various forms, consequences, and prevention measures is essential to protecting against cybercriminals. Stay vigilant, be cautious, and educate yourself and your organization to mitigate the risks associated with phishing.
FAQs (Frequently Asked Questions)
Phishing attacks primarily target individuals and organizations, aiming to steal personal information, financial data, and intellectual property.
Phishing emails often contain suspicious links, misspelled URLs, and urgent requests for personal information. Always verify the sender’s identity.
While businesses can suffer severe consequences, they are not typically held liable for being targeted by phishing attacks. However, they are responsible for protecting customer data.
Yes, engaging in phishing is illegal in most jurisdictions. Offenders can face fines and imprisonment.
You can report phishing attempts to your email provider, local law enforcement, and organizations like the Anti-Phishing Working Group (APWG) to help combat cybercrime.

 5G2 years ago
5G2 years agoHow 5G Technology Will Revolutionize Our Lives and Work

 Tech5 months ago
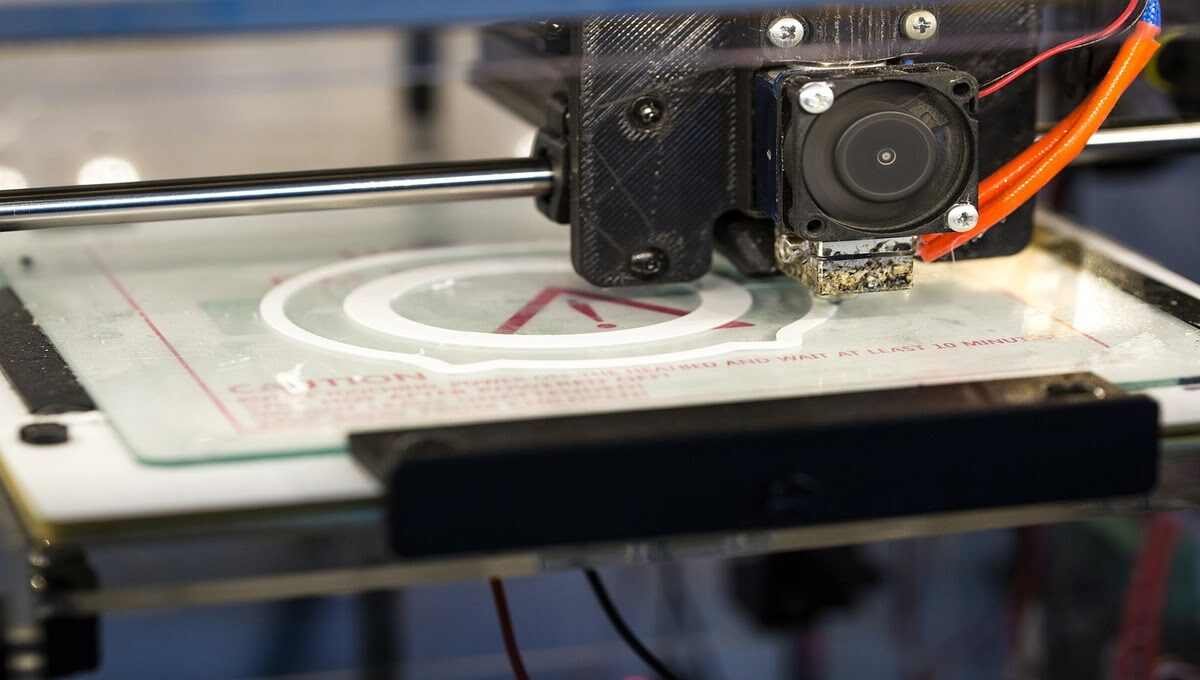
Tech5 months ago3d Printer Technology (Application) (History) And (Types)

 5G2 months ago
5G2 months agoWhat is the difference between 5G and 5G Plus?

 Computer1 year ago
Computer1 year ago“Bleeping Computer: Your Ultimate Guide to Cybersecurity”

 5G1 year ago
5G1 year agoDifference between 5G nsa and 5G sa

 5G1 year ago
5G1 year agoHow does 5g work on iPhone?

 5G1 year ago
5G1 year agoThe Future of 5G Technology : Revolutionizing Connectivity

 Tech1 year ago
Tech1 year agoExplain How Technology Has Affected People’s Activity Levels








tlover tonet
December 31, 2023 at 12:26 pm
I like what you guys are up too. Such smart work and reporting! Carry on the excellent works guys I have incorporated you guys to my blogroll. I think it will improve the value of my web site 🙂
Puravive
January 8, 2024 at 5:53 am
I loved you better than you would ever be able to express here. The picture is beautiful, and your wording is elegant; nonetheless, you read it in a short amount of time. I believe that you ought to give it another shot in the near future. If you make sure that this trek is safe, I will most likely try to do that again and again.